Here are 5 quick tips on how you can improve your personal IT security.
1. Set up Multi Factor Authentication where possible
MFA (Multi Factor Authentication) or 2FA (2 Factor Authentication) is becoming more and more common. When you log into a particular website or online tool using your username and password, a second factor of authentication will then be sent to your mobile device for verification.
This verification could come in the form of a phone call that you have to answer, a text that provides a code that you then have to input into the website, or a push notification that comes through on an app like Microsoft Authenticator or Google Authenticator.
This second form of authentication is a best effort to ensure you are who you say you are:
- You know the username
- You know the password
- You have the device that is registered against the above username/password
While this may not be totally fool proof, especially if your phone has been stolen and you have left your usernames & passwords somewhere easily accessible, it certainly reduces the scope of an intrusion into your account.
2. Follow good password etiquette
We have gone into this in more detail in our blog “Have I been Pwned”, but I’ll include a quick summary here.
- Try not to use the same password more than once.
- Use a password manager such as LastPass to help keep track of them.
- Don’t make your passwords personal e.g. pet names or favourite sports teams. These may be easily found on your social media pages.
- Do not share your passwords.
3. Make sure you have a good anti-virus system running on your devices
Anti-virus should now be an essential part of every user’s IT environment. We have now done numerous blogs over the past (here, here & here) year that have addressed some of the various nasties that are out there on the world wide web, waiting patiently to attack. Having an anti-virus program running at all times should be your first line of defence against them.
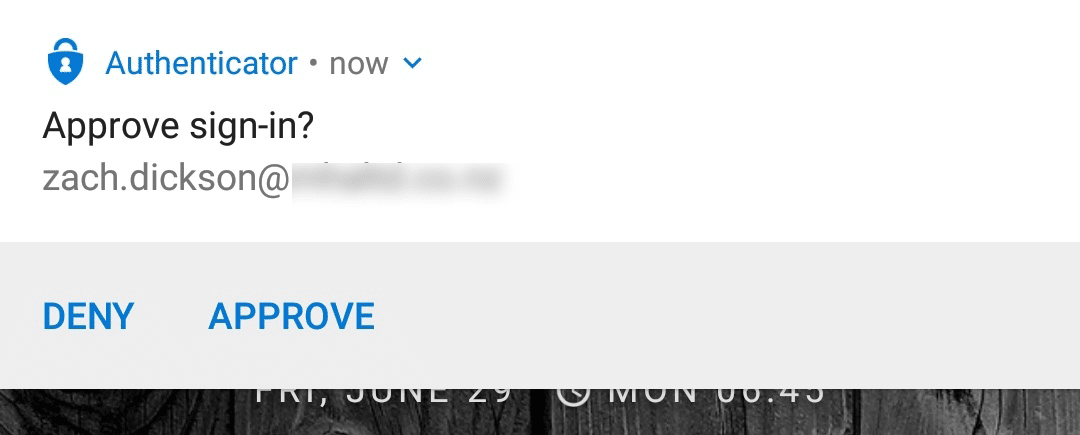
Lucidity offer SentinelOne, both as part of our Managed Desktop platform and as a service protecting end-user’s local devices. It utilises machine learning and AI to identify and neutralise a broad range of attacks.
SentinelOne offers up to $1million USD in warranty protection against ransomware attacks, so they are more than happy to put their money where their mouth is. It is classed as a visionary product on the Gartner Magic Quadrant for Endpoint Protection as well as scoring highly on their enterprise reviews.
4. Keep your devices up to date
This is an easy one that everyone should ensure they take seriously.
Update your devices when updates are available!
Whether it is your mobile, your PC, your Mac, your tablet – make sure they are always up to date. These updates often address security vulnerabilities that have been identified by the vendor and remove the vulnerabilities before they can be exploited.
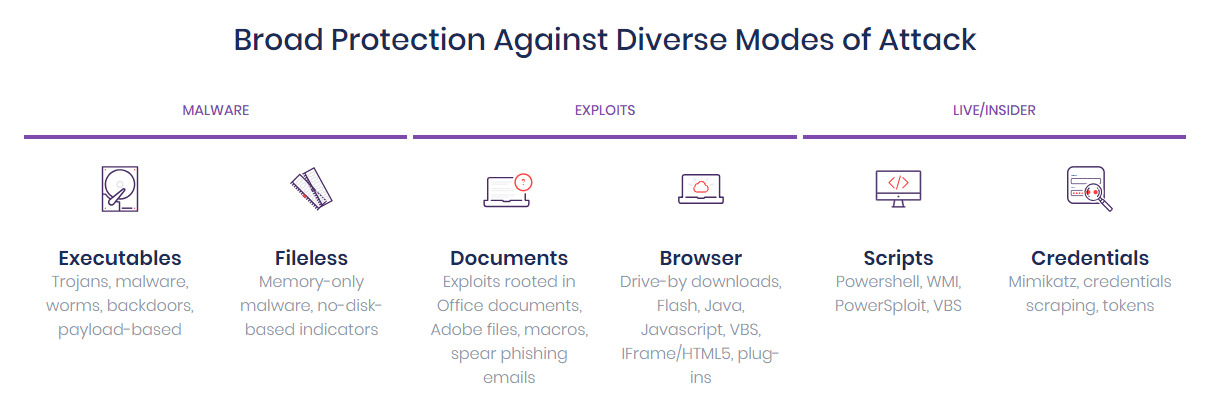
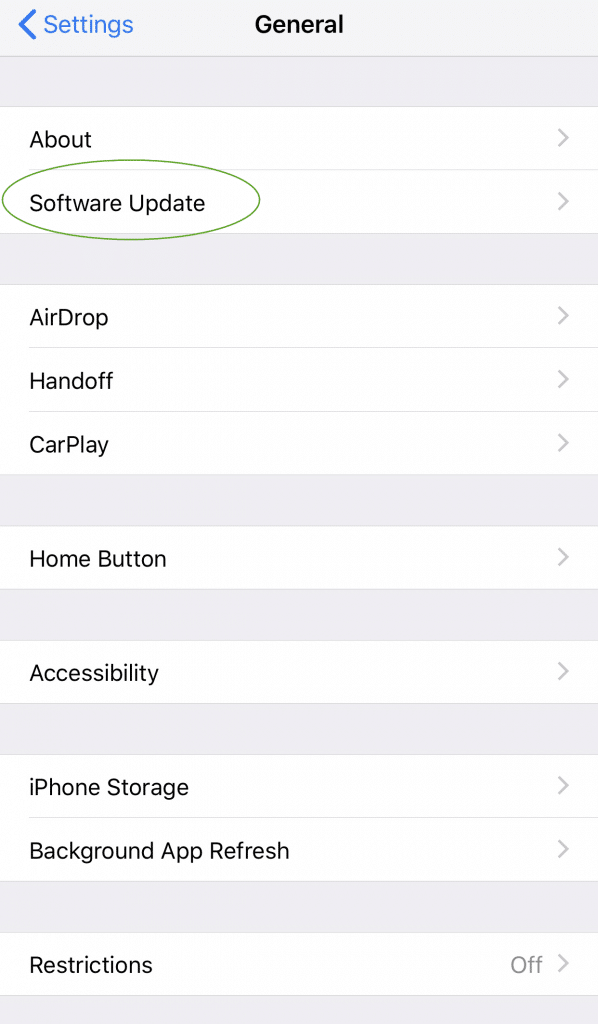
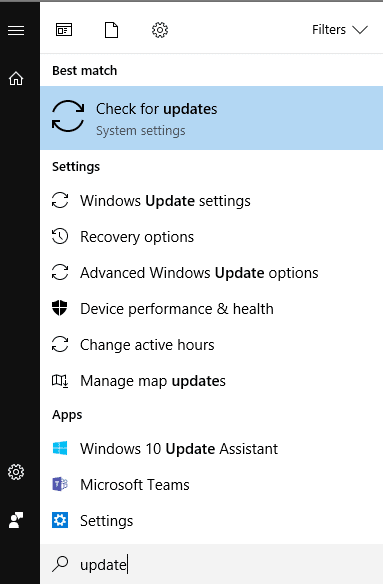
You will most likely receive notifications when updates are available but just in case, below are some screenshots of the best place to check if updates are available for your machine.
a. Android – Settings
b. Apple – Settings – General
c. Windows – Search for “Update” on the task bar
5. Secure your mobile device
With so much of our lives now living on our mobile devices, it is essential that these are protected from prying eyes should your phone be lost or stolen.
All mobile devices now have security options; many have fingerprint scanners, all will have PIN based passcodes and also patterns passcodes.
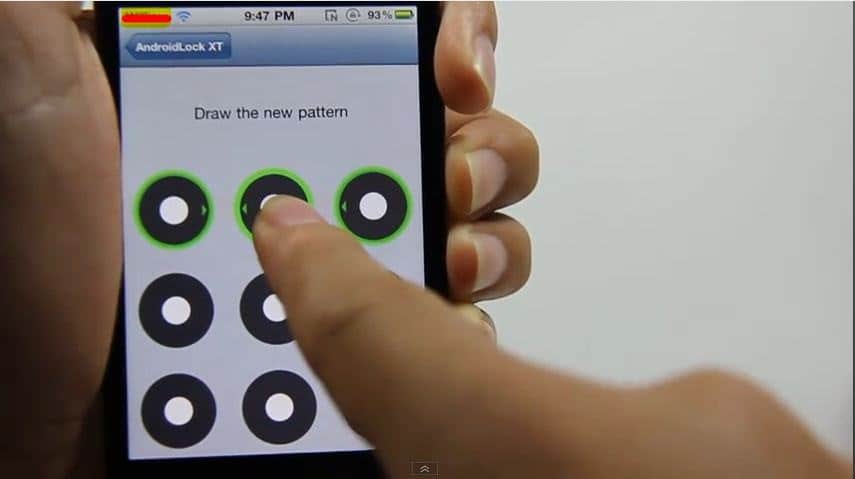
Make sure you are using one of these options on your mobile device. You can also set it up so that after a certain number of failed attempts, it will wipe your phone completely. This could be a good idea, especially if you have business sensitive information on your device.
Zach Dickson