Whaling is a specialised type of “Phishing”, for most of us this doesn’t really help explain what it is.
Phishing is the attempt to obtain sensitive information (user names and passwords, credit cards, personal details etc) which can then be used for malicious purposes – usually extracting money in some shape or form. (thanks Wikipedia for helping explain – note that this article is a good starting point for finding out more about the different types of Phishing attack.)
The annual worldwide impact is estimated to be in the billions of dollars, and it’s not all overseas – it really does impact New Zealanders on a daily basis.
Cyber criminals go “Phishing” by putting bait in front of people – commonly bait is in the form of emails which appear to come from legitimate or trusted sources, quite simply they are cleverly worded and succeed in getting poor unsuspecting people to click on links and enter information.

Whaling is a more serious type of Phishing that targets company owners/executives. Whaling attacks have the usual aim of deceiving large amounts of money from the organisation being targeted. Whaling is hence phishing, but for larger “Phish”. Generally, more time and effort goes into trying to catch a very large fish and the rewards for the criminals are more substantial.
Whaling is very real and happening on a daily basis. Even large companies with many controls in place have been caught out. Ubiquiti networks, a large NASDAQ listed technology company lost $47 million US dollars in 2015 via a whaling attack – the fraudster did a good job of impersonating the CEO via a quickly made gmail account, and sent a series of emails to the CFO instructing them to make a payment. The transfer of funds was made and the majority of funds were never recovered, more details in this article.
A bit closer to home, a few months ago, we experienced a direct attack. I was asked by our accounts payable to authorise a payment for $50,000 USD to be sent to an account in the USA – at this point, the payment was loaded and ready for my approval, shortly after I had an email from Paul (a fellow director of Lucidity) requesting that I authorise a payment for him. I smelt a rat and immediately called Paul who knew nothing about this payment and we were able to stop it there. On closer inspection his email had been falsified, the imposter had started up a clever conversation via email with our accounts department. Very clever, very simple and very effective.
I reported this to our bank who confirmed that this was commonly occurring and there wasn’t much that could be done about it. The scary thing is that all of the information needed to perform an attack such as this could be determined in less than 10 minutes by carrying out some simple research on the public internet.
A more complex attack may involve more in-depth analysis of a company’s operations. This starts by gaining access into a key person’s email.
The below example is the kind of “Phishing” email that might get sent to an individual, we have seen many of these being received in recent weeks. Ironically, Microsoft’s own Office 365 anti-spam service does not always detect these as malicious.
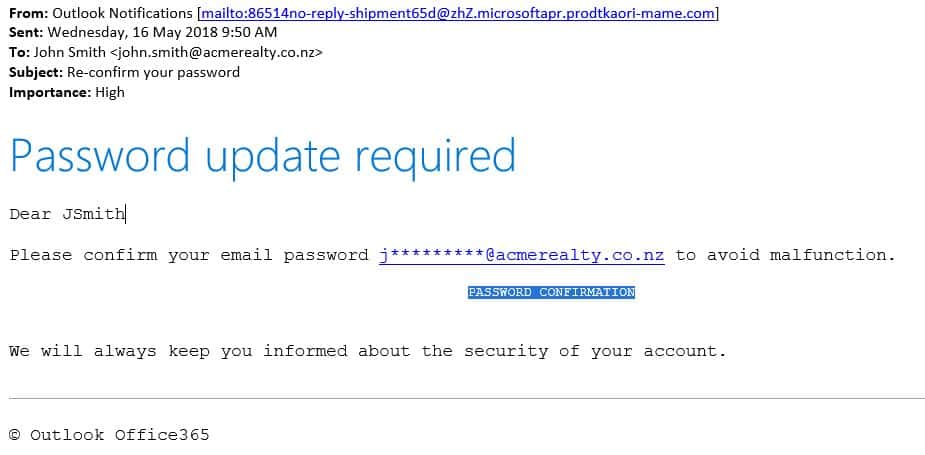
At first glance, it sort of passes as the kind of thing Microsoft might send you. The font and colours look familiar. Clicking on the password confirmation link (highlighted) will take you to a web page which may also look legitimate. The individual then enters their username and password and bingo – the criminal has all they need to access your email account. They can also sell your username and password to other criminals, who can then potentially use this to access other systems and services where you may have used the same username/password combination.
Looking more closely at the email:
- The from address is not a Microsoft owned address – it’s definitely not from Microsoft.
- This is fundamental – Microsoft would not send an email for you to do this.
It’s not hard to be fooled by this type of attack, always be very wary of where you are entering your password.
Despite the trust we place in each other at work, in today’s world we require more controls and measures to defend against these criminals. Fifty years ago they would have been bank robbers, today smart criminals steal millions of dollars without needing to leave home or even have much risk of being caught – they are getting away with it on a grand scale, it’s not getting any better and all sorts of businesses are being attacked every day.
Follow these steps to help protect yourself and your business:
Always be on high alert.
This happens every day to lots of people. Make sure everyone in your organisation is aware of how these scams work. You need to ensure security is continually front of mind.
Review your payment approval processes.
Ensure you have separation of responsibilities when it comes to approving payments. If not in place already – at least have one person approve payments, or if feasible, have two people approve payments over a certain amount.
Look for Spoofed emails.
Spoofing of email is common and easily done, if the topic of conversation via email is of poor quality or out of character language – verify directly and immediately via phone or in person. Even if the communication is from the correct email address, it's possible the account has been compromised and it is an imposter.
Two factor or Multi-Factor authentication (MFA)
MFA adds a second element to authentication, it can be an annoyance but helps ensure that only you are accessing your systems. For an imposter to get past this, they would also need your second factor of authentication (i.e. your mobile phone) – consider adopting MFA for your staff.
Passwords, Passwords, Passwords…
- Change passwords frequently (every 90 days minimum).
- Make passwords more complex and even multi-word.
- Don’t share passwords across personal and company accounts.
If you think this is a pain, read this article on passwords and think again, a short set of characters is all that is really protecting you against theft and fraud. If you don’t have MFA, make sure your password is very hard to guess.
Protect at the perimeter.
Advanced firewall technologies are networked and maintain an active database of the locations of fraudulent websites. This means that if a user clicks on a link, their access to the site will be blocked and they will be warned. This is not guaranteed, but it’s a very effective defence. We are a Fortinet partner and utilise Fortinet services to protect our customers as part of our Managed Desktop Service.
In summary, whaling and phishing are real and are compromising people and systems daily all over the world. Whaling and Phishing are types of social engineering, the criminals behind these operations are extremely clever and are carefree about the impact on you or society. Being aware and staying aware is the first step in protecting yourself.

Colin Williams